Key Cybersecurity Trends to Watch in 2024

Je suis un solution architecte dans le cloud Azure, avec des multiples expériences dans le monde du consulting. Je parcours l'univers informatique depuis déjà plus de 15 ans, m'amuse à jouer les magiciens du code et les alchimistes du cloud. J'ai été apprenti sorcier en conception des applications, et je fais partie des super-héros de développement backend, web et mobile, toujours prêt à sauver le monde du chaos informatique !
Mon pouvoir spécial réside dans l'art de construire des architectures gigantesques et de rendre les sites invincibles. Imaginez-moi, tel un maître des nuages, déployant des serveurs en un claquement de doigts et écrivant des sorts magiques pour des logiciels d'application éblouissants.
N'hésitez pas à me contacter si vous avez besoin d'aide ! Je suis toujours prêt à défendre l'Internet des méchants bugs et des pannes maléfiques ! :)
As we step into 2024, the landscape of cybersecurity is rapidly evolving. Staying ahead of these trends is crucial for building robust digital defenses. Here are the key cybersecurity trends that will shape the industry this year:
1. AI and Cybersecurity
Artificial Intelligence (AI) is becoming increasingly vital in cybersecurity. By analyzing vast amounts of data, AI can detect threats that humans might miss. It automates repetitive tasks and provides predictive insights, shifting from reactive to proactive security measures.
Advantages:
Advanced Threat Detection: AI can identify patterns and anomalies in real-time, enabling quick responses.
Automation: AI systems can automate repetitive tasks, freeing up human resources for more complex threats.
Challenges:
Exploitation Risks: AI systems themselves can be targeted and exploited by malicious actors.
Skill Requirements: Integrating AI into cybersecurity requires specialized skills and ongoing training for security professionals (ISACA).
2. Remote Work Security
The rise of remote work, initially driven by the COVID-19 pandemic, continues to expand. This trend brings unique cybersecurity challenges as home networks and personal devices are often less secure than corporate environments.
Key Considerations:
Secure Access: Ensure that remote connections are secured with VPNs and robust encryption protocols.
Training and Awareness: Employees need to be trained to recognize potential threats and follow best security practices (Splashtop).
3. Mobile Security
The increasing use of mobile devices for both personal and professional tasks presents unique security challenges. Every mobile app can potentially be a vulnerability.
Strategies:
Data Encryption: Protect data in transit and at rest on mobile devices.
Mobile Device Management (MDM): Utilize MDM solutions to control and secure devices accessing corporate resources (Splashtop).
4. IoT Security
The Internet of Things (IoT) connects everyday objects to the internet, expanding the attack surface. Each connected device can be a potential entry point for cyberattacks.
Measures:
Regular Updates: Ensure all IoT devices are regularly updated with the latest security patches.
Network Segmentation: Separate IoT devices from the main network to limit the impact of a breach (ISACA).
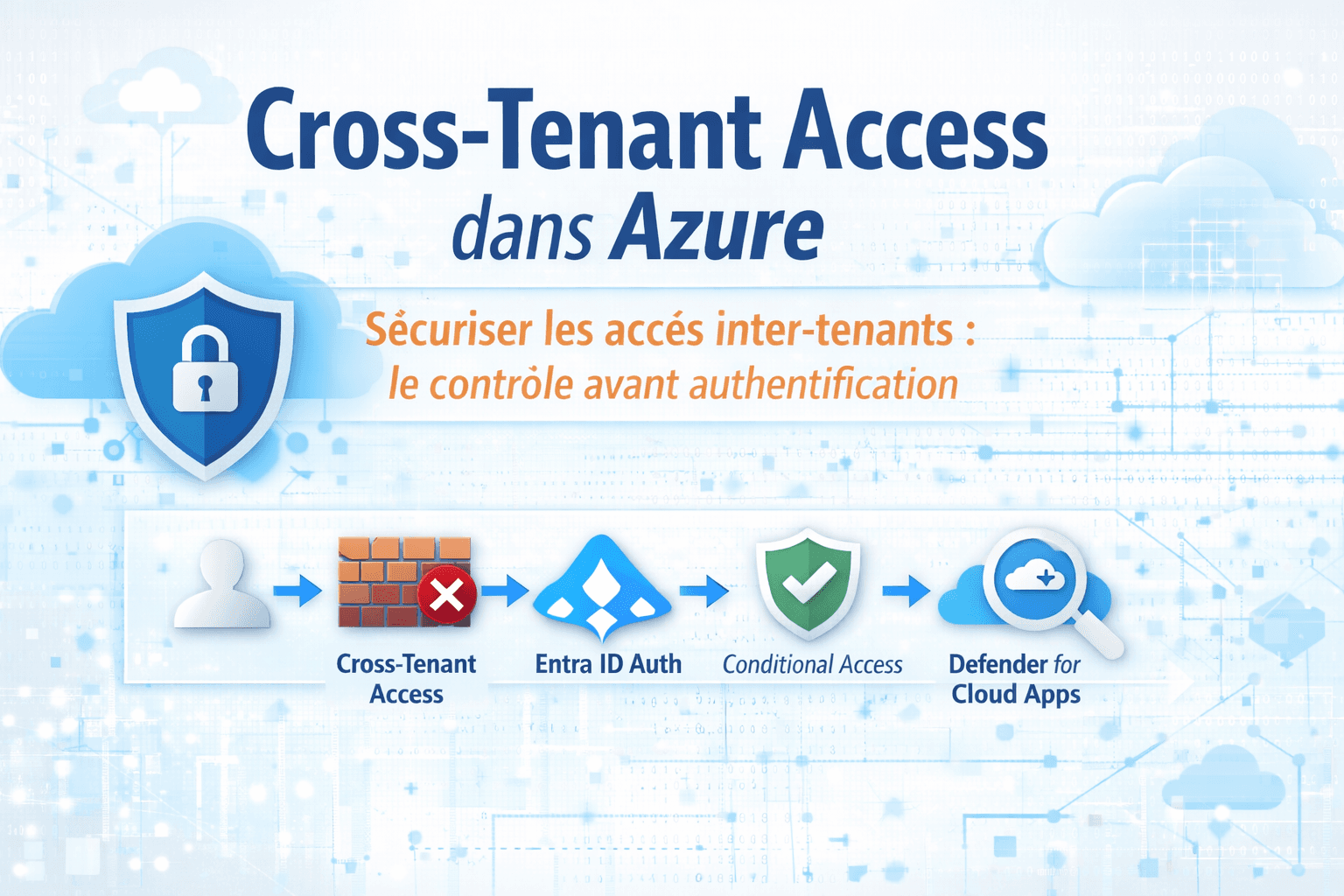
5. Cloud Security and Compliance
The shift to cloud-based solutions continues to accelerate, offering significant benefits in scalability and cost. However, this shift necessitates enhanced security and compliance measures to protect sensitive data stored and processed in the cloud.
Best Practices:
Compliance Automation: Use tools to automate compliance processes and reduce human error.
Data Security: Implement strong encryption protocols and strict access controls to protect sensitive data (Splashtop).
6. Evolving Phishing Attacks
Phishing attacks are becoming more sophisticated, making traditional security measures less effective. These attacks are now more targeted and use advanced techniques to deceive users.
Solutions:
Multi-Factor Authentication (MFA): Implement MFA systems to add an extra layer of security.
Continuous Awareness Training: Educate users to recognize phishing attempts and respond appropriately (Splashtop).
7. Quantum Computing
Quantum computing promises to revolutionize many fields, including cybersecurity. However, it also poses significant challenges to current cryptographic systems.
Preparations:
Quantum-Resistant Cryptography: Develop and adopt algorithms that can withstand quantum computing capabilities.
Continuous Monitoring: Stay informed about advancements in quantum computing and adapt security strategies accordingly (Splashtop).
Conclusion
In 2024, cybersecurity must be a top priority for all organizations. The identified trends highlight the importance of adopting a proactive and adaptable approach to protect our digital environments. Cloud security, in particular, should be a focus to ensure data protection and regulatory compliance.
By monitoring these trends and implementing appropriate strategies, we can better safeguard against emerging cyber threats. Together, we can work towards a safer digital future.
Sources: